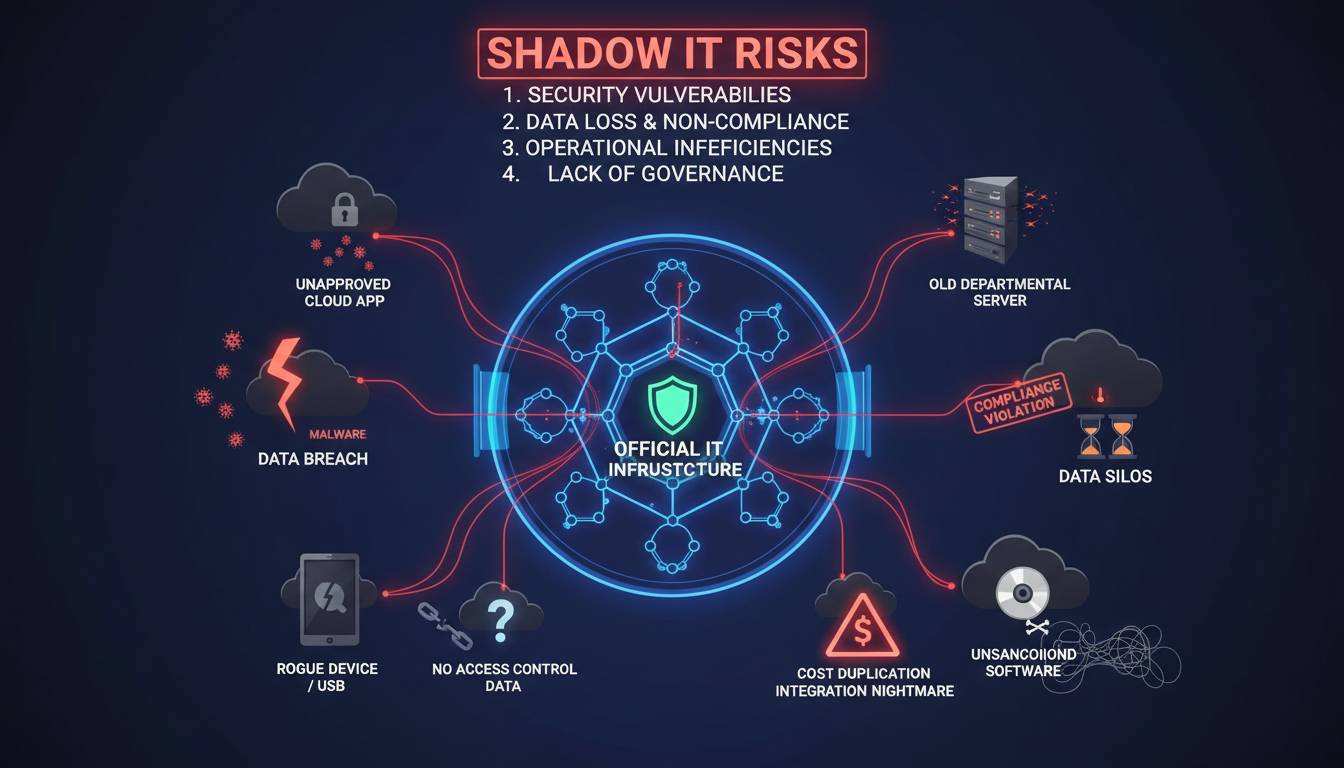
Shadow IT refers to information technology systems and solutions built and deployed inside organizations without explicit approval from the IT department. These unauthorized tools—ranging from cloud storage services and messaging apps to custom software and personal devices used for work purposes—operate outside the visibility and governance of the organization’s formal IT infrastructure. While employees often adopt these tools to improve productivity or solve immediate problems, the resulting fragmentation creates significant security vulnerabilities, compliance gaps, and management challenges that can outweigh any short-term efficiency gains.
Understanding Shadow IT: Definition and Scope
The term Shadow IT describes technology infrastructure that exists within an organization without the knowledge or approval of the central IT function. This differs from sanctioned IT, where the organization deliberately selects, implements, maintains, and monitors specific tools and platforms according to established security and operational standards. Shadow IT emerges when departments, teams, or individual employees procure and deploy solutions to address specific needs—often faster than the formal IT procurement process allows—without going through security reviews, compliance checks, or architectural oversight.
The scope of Shadow IT has grown significantly in recent years. What once meant employees installing unauthorized software on office computers now encompasses an entire ecosystem of cloud-based services, mobile applications, personal devices connecting to corporate networks, and even AI tools that employees use without IT awareness. The rise of software-as-a-service (SaaS) has accelerated this trend. A marketing team can sign up for a new project management tool in minutes using a corporate credit card, bypassing the months-long evaluation process that formal IT procurement would require. Similarly, a development team might adopt a new coding framework or cloud service to speed up delivery, only later discovering that the tool stores data in a region that violates data residency requirements.
Industry analysts estimate that Shadow IT spending can account for 30% to 50% of total IT spending in certain industries. The reasons employees cite for adopting unsanctioned tools typically center on speed, usability, and the perception that formal IT processes move too slowly to meet business needs. A sales team might adopt a particular CRM tool because it integrates more naturally with a vendor they already use, while the engineering department might prefer a specific development environment that the IT security team has not yet approved. These decisions, made with good intentions at the team level, accumulate into an organizational technology landscape that leadership cannot fully see or control.
The tension underlying Shadow IT reflects a broader challenge in modern organizations: the desire for agility and responsiveness at the team level conflicts with the organization’s need for centralized visibility, security, and governance. Employees experience the IT approval process as bureaucratic friction that slows their work. IT departments face the impossible task of evaluating and securing every tool that every employee might want to use. This tension has no easy resolution, but organizations that ignore it entirely do so at significant risk.
Why Shadow IT Creates Security Risks
The security implications of Shadow IT represent perhaps the most immediate consequence of unmanaged technology proliferation. When employees use unsanctioned tools to handle business data, they often bypass the security controls that the organization has carefully implemented. These controls might include data encryption standards, multi-factor authentication requirements, network segmentation policies, and incident response procedures. A Shadow IT solution may implement none of these protections, or implement them in ways that meet no organizational standard.
Data leakage ranks among the most severe risks. Consider a scenario where a team adopts a free file-sharing service to collaborate on a project involving sensitive financial information. The files uploaded to that service reside on infrastructure the organization does not control, may be accessible from any device with internet access, and likely reside in data centers subject to different jurisdictional laws. When that service experiences a breach—something that happens regularly across the technology industry—the organization has no way to know what data has been exposed, no contractual ability to require notification, and no recourse to enforce remediation. The organization may learn about the breach only when it appears in news reports or when regulators come calling.
Compliance violations represent another major concern. Organizations in regulated industries—healthcare, financial services, government contracting, and many others—face strict requirements around how they handle and protect sensitive data. Regulations such as HIPAA, PCI DSS, and GDPR impose specific obligations on technology choices, data handling, and breach notification. When employees use Shadow IT to process regulated data, they may inadvertently place the organization in violation of these requirements. The consequences can include substantial financial penalties, mandatory audits, reputational damage, and in extreme cases, the loss of operating licenses or contracts.
The attack surface of an organization expands significantly with Shadow IT. Each unauthorized application, service, or device connected to corporate resources represents a potential entry point for malicious actors. Attackers actively scan for vulnerable services, and the particular appeal of Shadow IT to attackers lies in its relative invisibility to security teams. A shadow cloud instance with outdated software and default credentials might sit undetected for months, providing a persistent foothold that attackers can exploit to move laterally through the network. The organization cannot defend what it cannot see, and Shadow IT by definition operates outside the visibility of defensive teams.
Common Examples of Shadow IT in Organizations
Shadow IT manifests across virtually every category of enterprise technology. Understanding the most common forms helps organizations know where to look when attempting to discover and manage these risks.
Unsanctioned cloud services constitute perhaps the most prevalent form. Employees sign up for cloud-based productivity tools, project management platforms, file-sharing services, communication applications, and dozens of other categories using personal accounts or company credentials that no one in IT approved. A sales team might adopt a particular video conferencing platform because it offers features they prefer. The marketing department might use a design tool that requires no installation but stores creative assets on external servers. Engineering teams frequently adopt development tools, code repositories, and testing frameworks without IT involvement. Each of these services processes business data, yet operates outside the organization’s security monitoring and governance framework.
Personal devices used for work purposes represent another common form of Shadow IT. When employees access corporate email, documents, and applications from personal smartphones, tablets, or laptops, they create unmanaged access points to sensitive resources. These devices may lack security software, operating system updates, or encryption that the organization would require if the devices were corporate-owned. The bring-your-own-device (BYOD) trend, while offering legitimate business benefits, creates Shadow IT challenges that many organizations struggle to manage effectively.
AI tools have emerged as a significant concern in recent years. As generative AI platforms have become widely available, employees have rapidly adopted them for tasks ranging from drafting communications to analyzing data to writing code. Many of these AI tools process input data in ways that may create intellectual property or data confidentiality concerns. An employee might paste sensitive business information into an AI assistant without understanding where that data goes or how it might be retained and used to train future models. The rapid adoption of these tools has outpaced most organizations’ ability to develop policies and controls, creating a substantial and growing category of Shadow IT risk.
Unapproved hardware also falls within the Shadow IT definition. This includes personal devices brought into the office and connected to the network, network equipment installed by departments without IT involvement, Internet of Things (IoT) devices deployed by facilities or operations teams, and storage devices connected to corporate systems. A facilities team might install smart sensors throughout a building without coordinating with IT security, creating potential entry points that attackers can use to access more sensitive network segments.
How to Discover and Manage Shadow IT
Discovering Shadow IT requires a multi-faceted approach because the whole point of Shadow IT is that it operates outside normal visibility channels. Organizations cannot rely solely on employees self-reporting their use of unsanctioned tools—employees often do not realize they are creating risk, or they may actively avoid reporting because they fear losing access to tools they find valuable.
Network traffic analysis provides one of the most effective discovery methods. By monitoring what traffic leaves the corporate network and where it goes, security teams can identify connections to unknown cloud services, suspicious IP addresses, and unusual data transfer patterns. Organizations that implement cloud access security brokers (CASBs) or network monitoring tools often discover that their users are communicating with hundreds or thousands of cloud services that the IT department has never heard of. This visibility represents a critical first step toward managing the risk.
Cloud access security brokers and security information and event management (SIEM) systems can correlate data from multiple sources to build a comprehensive picture of technology usage across the organization. These tools can identify Shadow IT by detecting authentication events to unknown services, unusual data exfiltration patterns, or applications that are accessed frequently but have no corresponding asset record in the IT inventory.
Regular audits and assessments complement technical discovery methods. This includes periodic reviews of credit card statements to identify subscriptions for services that are not in the IT inventory, surveys or interviews with department heads about the tools their teams use, and review of procurement records to catch purchases that bypassed formal channels. Many organizations are surprised by what these audits reveal.
Employee engagement matters at least as much as technical detection. When employees understand why certain controls exist and feel that their needs are heard, they are more likely to collaborate with IT rather than work around it. Creating clear, accessible processes for requesting and approving new tools removes the friction that drives employees toward Shadow IT in the first place. If the approval process takes months, employees will find workarounds. If the process is transparent and reasonably fast, more employees will use it.
Once discovered, managing Shadow IT requires nuanced judgment. Not every unsanctioned tool represents unacceptable risk, and outright banning tools without providing alternatives simply drives them further underground. The goal should be to bring Shadow IT into the light, evaluate each solution against security and compliance requirements, and either formally approve and integrate it into the IT portfolio or work with the team to transition to a sanctioned alternative that meets their needs.
Building a Governance Framework for Shadow IT
Effective Shadow IT management requires more than detection—it requires a governance framework that balances business agility with security and compliance needs. This framework should establish clear policies about which categories of tools require approval, what security standards they must meet, and what process employees should follow when they need a new solution.
The framework should distinguish between different risk levels. Low-risk tools—basic productivity applications that handle no sensitive data—might require only registration in a catalog. High-risk tools—those that process regulated data, connect to critical systems, or store significant business information—should require formal security review before approval. This tiered approach ensures that IT attention focuses where it matters most, rather than getting bogged down reviewing every minor application.
Documentation and inventory represent foundational elements. Organizations cannot govern what they do not know about. Maintaining a current inventory of all approved tools, their owners, the data they process, and their security controls enables risk management, incident response, and compliance reporting. When a vulnerability affects a particular software product, the organization needs to know whether that product is in use and who is responsible for addressing it.
Training and awareness programs help employees understand the reasoning behind the policies. Many Shadow IT situations arise not from malicious disregard for security but from simple lack of awareness. When employees understand that Shadow IT can create genuine risks for the organization and their colleagues, they become partners in managing the problem rather than unwitting contributors to it.
Looking Ahead: The Evolving Shadow IT Challenge
The challenge of Shadow IT will not diminish—it will intensify. Technology continues to become more accessible, more powerful, and easier to adopt without specialized knowledge. The barriers to spinning up a cloud service, downloading a development tool, or connecting a new device continue to fall. Organizations that treat Shadow IT as a solved problem will find themselves increasingly vulnerable.
The most resilient organizations will be those that acknowledge the fundamental tension between agility and control and build adaptive governance approaches that accommodate both. This means investing in detection capabilities, streamlining approval processes, educating employees, and maintaining honest internal conversations about what is achievable and what tradeoffs are acceptable. The organizations that pretend Shadow IT does not exist, or that believe policy alone can eliminate it, are the ones that will suffer the most severe consequences when their hidden risks materialize into security incidents, compliance violations, or data breaches.